Overview
Learn about how you can enhance your Cilium setup with Gloo Network for Cilium.
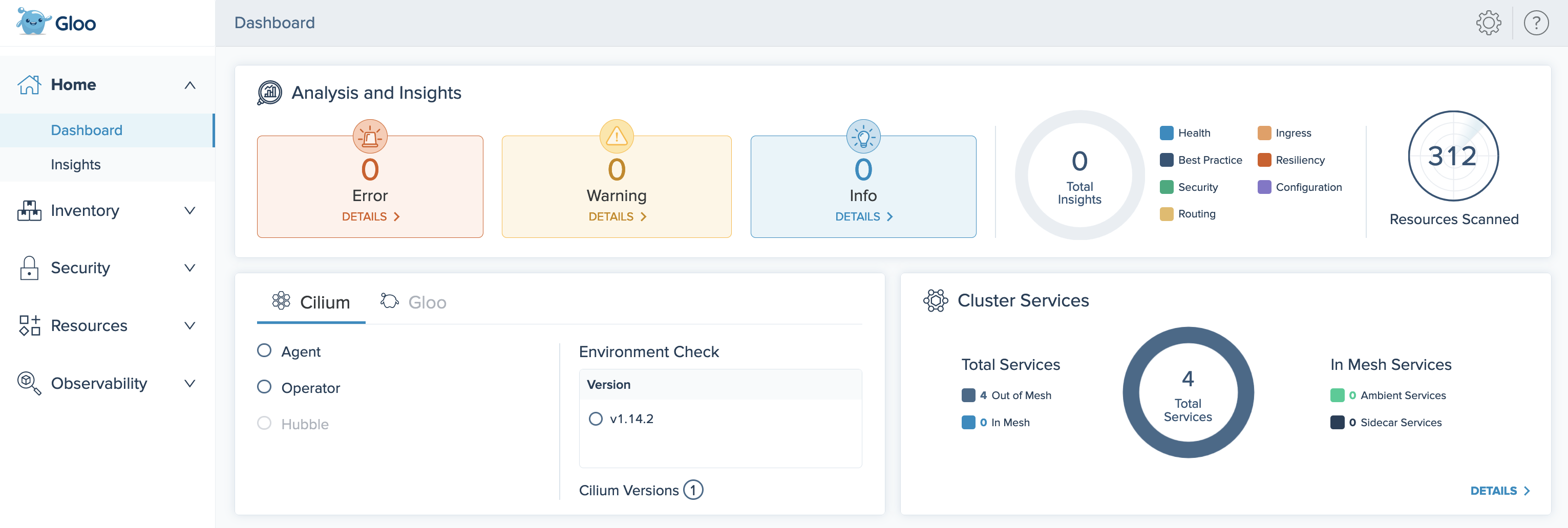
Gloo Network for Cilium works with community Cilium out of the box. You get instant insights into your Cilium environment through a custom dashboard. Observability pipelines let you analyze many data sources that you already have.
But Gloo Network includes more than tooling to complement an existing Cilium installation. You can also replace community Cilium with Solo’s hardened Cilium images. These images unlock enterprise-level support. Later, you might choose to upgrade seamlessly to Gloo Mesh Enterprise for a full-stack service mesh and API gateway solution. This approach lets you scale as you need more advanced routing and security features. For more information about these components, see Architecture.
Enterprise support
Gloo Network provides Solo distributions of Cilium images to provide connectivity, security, and observability for containerized workloads with a Cilium-based container network interface (CNI) plug-in that leverages the Linux kernel technology eBPF. The Solo distribution of Cilium is a hardened Cilium enterprise image, which maintains support for security patches to address Common Vulnerabilities and Exposures (CVEs) and other security fixes. Additionally, Gloo Network generates insights to help you evaluate the health and configuration of your Cilium setup. To install the Cilium CNI with a Solo image, see the quickstart or Helm installation guides.
| Benefit | Description |
|---|---|
| Enhanced performance | Instead of using iptables rules to route traffic in a cluster, Gloo Network uses the kernel technology eBPF to shorten the data path of a packet. With eBPF, packets to and from apps can be directly forwarded and written to the socket of the target app. This setup reduces network latency and the necessary packet processing in the kernel as the TCP/IP stack in the OSI network model is bypassed. In addition, you decrease CPU and memory overhead on your cluster worker nodes, and can use the freed up resources to manage cluster workloads more efficiently. |
| N-4 version support for Cilium | Gloo Network includes n-4 Cilium version support with security patches to address Common Vulnerabilities and Exposures (CVEs) starting with the first Gloo Network release. |
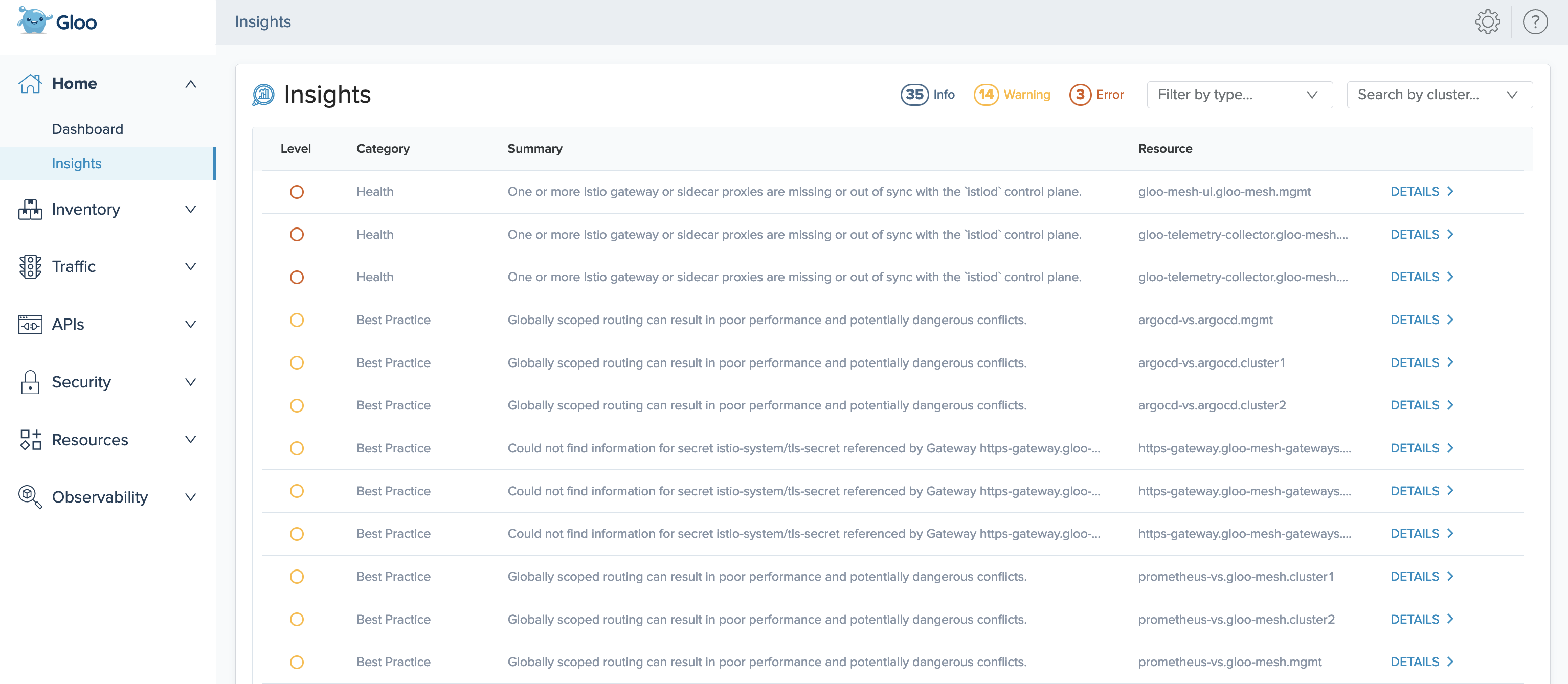
| Cilium insights | Evaluate the health, performance, and security posture of your Cilium setup with Gloo Network insights, and get recommendations for how to harden Cilium components, such as the Cilium agent. |
| Built-in observability tools | Gloo Network provides out-of-the-box observability tools, such as the Gloo UI, Prometheus, and Grafana. You can use these tools to gain visibility into the health of your Cilium setup, monitor network traffic in the cluster, and debug Cilium network policies. |
Operational observability
Gloo Network uses the OpenTelemetry (OTel) project to collect telemetry data from many sources in your clusters. Some of these sources, such as Grafana and Prometheus, are built in to monitor your Gloo environment and the apps in your cluster. You might have other existing sources, too. With OTel, you can set up pipelines for these sources as needed, so that you have all your telemetry data in a single place.
The Gloo UI shows these observability details in a single pane of glass, as shown in the following figure. For more information, see Telemetry.
Insights
Gloo Network comes with an insights engine that automatically analyzes your Cilium setup for health issues. Then, Gloo shares these issues along with recommendations to harden your Cilium setup. The insights give you a checklist to address issues that might otherwise be hard to detect across your environment. For example, insights can help you identify:
- Nodes in your Cilium environment that are unreachable
- eBPF map pressure
- Packet drops due to connection table issues
- When the number of Cilium identities approaches the limit
- IP address allocation and exhaustion
You can view the list of insights for your environment by opening the Insights page of the Gloo UI. For more information, see Insights.
Seamless migration to full-stack service mesh
Gloo Network provides a core set of tooling to help you observe and manage your Cilium setup. As you continue to scale your environment, you might have increasingly complex app networking problems. You can seamlessly migrate from Gloo Network for Cilium to Gloo Mesh Enterprise. With Enterprise, you get a full-stack L4-L7 app networking solution. Then, you can manage API gateways and service meshes in complex, multicluster environments.
Unlock Gloo’s powerful custom resources for advanced features including the following:
- Solo distribution of Istio support and Istio service mesh lifecycle management
- Automatic discovery of Istio resources across cluster
- Envoy-based ingress and egress gateways
- East-west gateway for cross-cluster communications
- Gloo workspaces for simple multitenancy
- Gloo virtual gateways and route tables to manage cross-cluster application routing
- All Gloo policies to build zero-trust security into your networking
- Automatic translation of Gloo policies into Cilium network policies
- Hardened external auth and rate limiting servers
- Gloo external services to bring in workloads in external VMs to the mesh
- GraphQL server built into ingress gateway
- Developer portal to share and monetize your APIs
- Ability to route to AWS Lambdas
For more information, see the Gloo Mesh Enterprise docs.